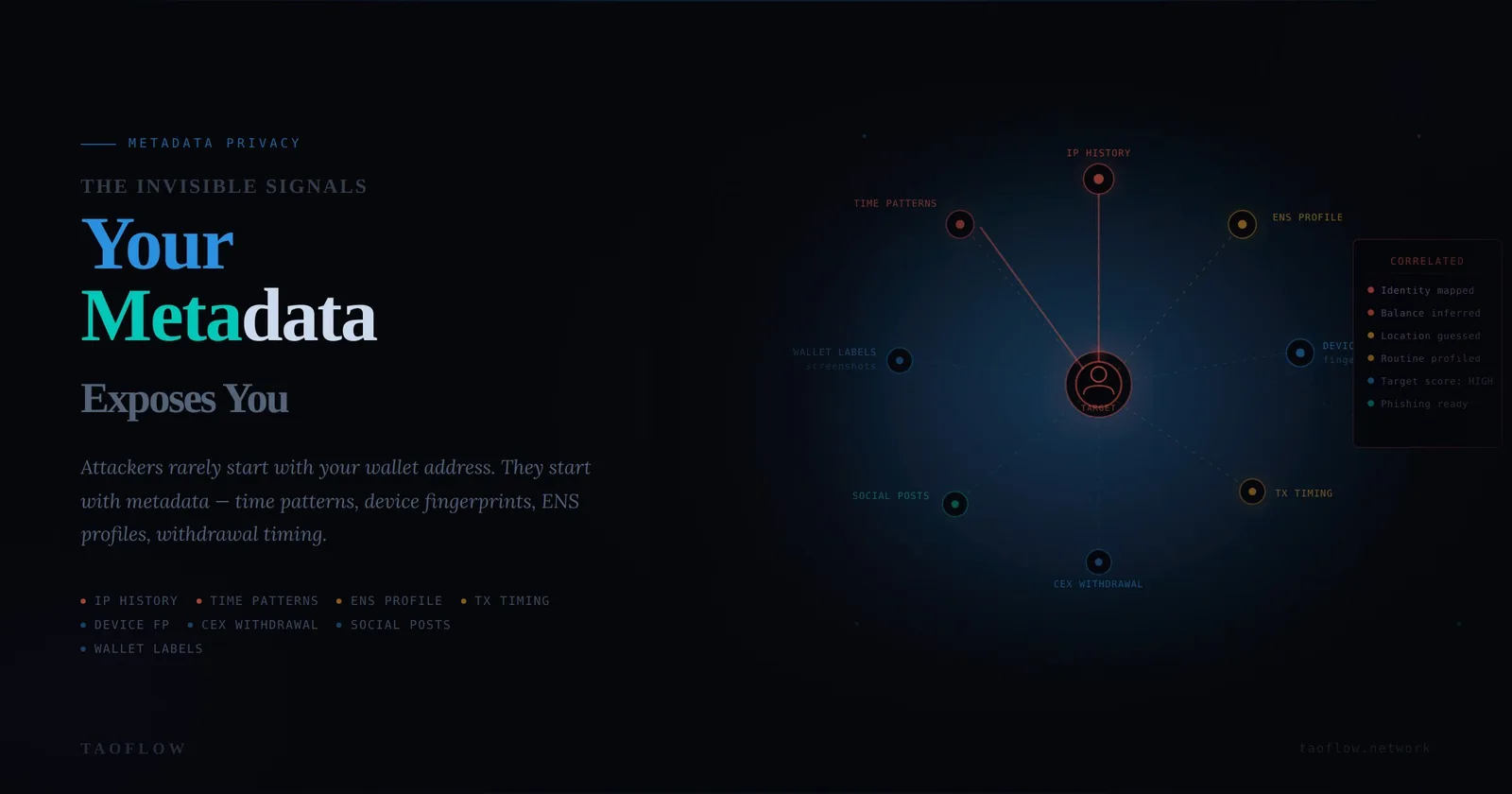
Most crypto users think privacy starts and ends with wallet addresses. In practice, attackers often start somewhere else: metadata.
Metadata is the context around your activity—time patterns, device fingerprints, IP history, ENS profiles, exchange withdrawal timing, social posts, and even how you name wallet labels in screenshots. Any one signal may seem harmless. Combined, they can identify you, map your balances, and make you a better target for phishing, extortion, or physical coercion.
This guide focuses on practical habits, not paranoia. The goal is simple: make correlation harder and mistakes rarer.
Threat Model: Who Uses Your Metadata and Why
Before changing tools, define your likely adversaries:
-
Opportunistic scammers They look for public clues to craft believable phishing messages.
-
Targeted social engineers They correlate your on-chain activity with social identity, employer, city, or routine.
-
Data brokers and analytics firms They aggregate cross-platform behavior and sell enriched profiles.
-
Criminal actors They prioritize victims with visible holdings and predictable behavior.
If your threat model includes (2) or (4), metadata discipline matters as much as seed phrase safety.
Where Metadata Leaks Usually Happen
1) Network layer
- Reusing the same IP context for exchange, wallet actions, and public browsing.
- Signing sensitive transactions on untrusted or inconsistent networks.
2) Identity layer
- Reusing one handle/email across forums, governance, and exchange-linked accounts.
- Publicly tying ENS/domain names to personal profiles.
3) Behavior layer
- Regular transfer sizes and timing that mirror salary or business cycles.
- Posting "just aped" screenshots right after execution.
4) Device layer
- Same browser profile for research, social media, and transaction signing.
- Leaky extensions and broad clipboard/history access.
5) Communication layer
- Sharing transaction hashes in public channels with identifying context.
- Forwarding wallet screenshots with visible tabs, bookmarks, or notifications.
The 20-Minute Metadata Hygiene Routine (Weekly)
Use this as a recurring checklist.
Step A: Account and identity separation (5 minutes)
- Verify you are not reusing primary personal email for crypto-critical accounts.
- Review social bios for wallet names, ENS domains, exchange hints, or portfolio clues.
- Remove unnecessary cross-links between your public identity and crypto activity.
Step B: Wallet context separation (5 minutes)
- Split wallets by role: long-term storage, active trading, experimentation.
- Confirm each role has distinct interaction patterns and counterparties where possible.
- Avoid moving funds in obvious linear paths right after KYC exchange withdrawals.
Step C: Device/browser hygiene (5 minutes)
- Use a dedicated browser profile (or separate device) for signing.
- Remove unused extensions; audit permissions for those that remain.
- Clear stale sessions on dashboards and revoke old dApp approvals.
Step D: Communication hygiene (5 minutes)
- Sanitize screenshots before sharing (tabs, bookmarks, balances, time, notifications).
- Delay posting trade actions; avoid real-time “I just did X” signals.
- Never share full operational flow in one public post.
Practical Rules That Reduce Correlation Fast
-
Time-shift disclosures If you discuss a move publicly, do it later—not at execution time.
-
Standardize transfer behavior Randomized but bounded timing and amount patterns reduce easy clustering.
-
Segment wallet purpose Don’t mix governance identity, public social identity, and treasury behavior in one address set.
-
Treat explorer notes as public forever Any label or memo can become attribution evidence later.
-
Audit your own footprint monthly Search your handles + ENS + known wallet snippets and record what is exposed.
Incident Signals: When to Assume Your Metadata Is Burned
Act quickly if you notice:
- Highly specific phishing messages referencing your recent on-chain actions.
- New scam DMs shortly after public wallet interactions.
- Attempts to reset exchange or email accounts after large transfers.
- Doxxing hints combining crypto activity with personal details.
If two or more signals appear in the same week, treat it as active targeting.
48-Hour Containment Plan
If metadata exposure is suspected:
First 6 hours
- Pause non-essential transactions.
- Rotate passwords on email, exchange, and key social accounts.
- Enable or re-verify phishing-resistant MFA where available.
- Revoke high-risk dApp approvals.
6–24 hours
- Move critical assets to pre-prepared, clean destination wallets.
- Reduce public posting cadence about crypto activity.
- Notify close collaborators not to reveal your wallet mappings.
24–48 hours
- Rebuild wallet role separation map.
- Document root cause (what signal likely linked identity and wallet behavior).
- Add one new permanent control (e.g., dedicated signing browser profile, stricter posting delay).
A Lightweight Tooling Baseline
You do not need a complex stack to improve privacy. A minimal baseline:
- One dedicated signing environment.
- One documented wallet-role map.
- One weekly metadata checklist.
- One incident containment playbook saved offline.
For users who want cleaner network-context separation without heavy setup overhead, TaoFlow can be one optional component in that baseline—but process discipline is still the main defense.
Final Checklist (Copy/Paste)
- [ ] Wallets split by role and risk
- [ ] Public profiles scrubbed of direct wallet links
- [ ] Dedicated signing browser/device verified
- [ ] Extension permissions reviewed this week
- [ ] Old dApp approvals revoked
- [ ] Screenshot sharing sanitized
- [ ] Trade/action posts delayed
- [ ] Monthly self-dox search completed
- [ ] 48-hour containment plan updated
Privacy in crypto is rarely one magic tool. It is the sum of repeatable habits that deny attackers easy correlations.