Phishing in crypto rarely looks like a scam at first glance. It looks like urgency, familiarity, and convenience: a Discord mod asking you to "reconnect," a wallet popup that appears during a normal mint, or a friend account forwarding a "new staking portal."
Most losses happen in minutes, but the setup starts earlier: attackers train you to trust speed over verification.
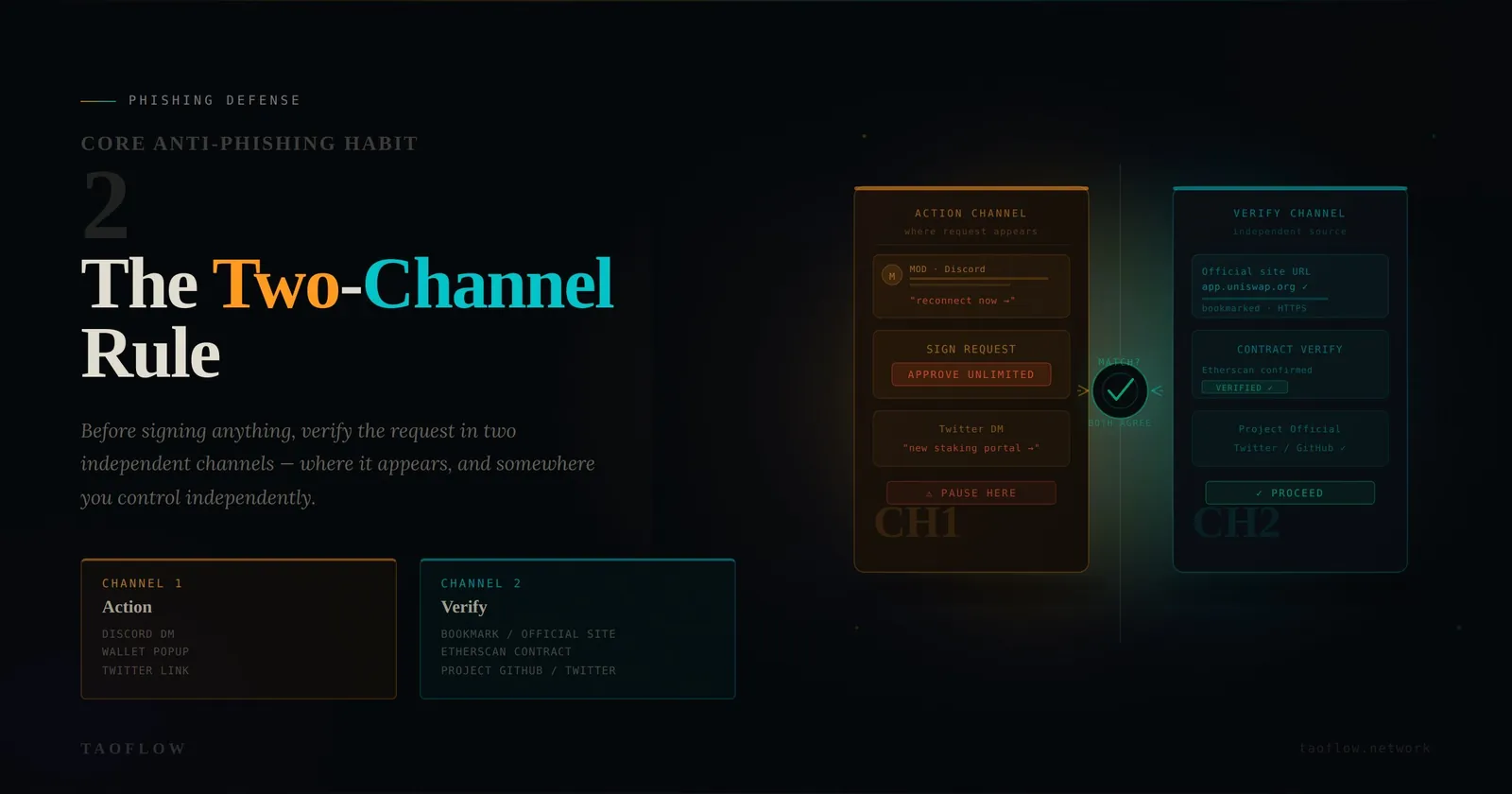
This guide gives you one habit that dramatically lowers risk: the Two-Channel Rule.
The Two-Channel Rule (Core Habit)
Before approving any high-impact action (signature, seed phrase entry, API key creation, withdrawal confirmation), verify the request in two independent channels:
- Action Channel: where the request appears (website, DM, Telegram group, email).
- Verification Channel: a separate source you navigate to yourself (official docs, pinned announcement, known admin handle, bookmarked domain, on-chain explorer).
If both channels do not match, you stop.
This sounds simple, but it defeats most real-world phishing because attackers usually control only one channel at a time.
Threat Model: What Attackers Exploit
Attackers usually win with one of four levers:
- Time pressure: "Airdrop ends in 8 minutes."
- Authority mimicry: fake support account, cloned X profile, copied logo.
- Interface familiarity: near-identical domain and wallet prompt wording.
- Social proof: botted replies, fake "worked for me" comments.
Your defense is not "being careful." Your defense is a repeatable verification workflow that still works when you are tired or distracted.
A 90-Second Pre-Sign Checklist
Use this every time a signature could move funds, grant approvals, or expose account control.
1) Stop the timer
If the message creates urgency, assume risk increased. Take 90 seconds before any click.
2) Re-open from your own bookmark
Never trust links from chat. Manually open the project from your saved bookmark or typed domain.
3) Compare exact domain string
Check full domain, not just brand text. Watch for swapped letters, extra subdomains, or unusual TLDs.
4) Verify contract address out-of-band
Match contract addresses against at least one independent source (official docs + explorer labels, or docs + verified social announcement).
5) Read wallet prompt semantics
Reject blind signing whenever possible. If message bytes are unreadable and the action is not expected, cancel.
6) Inspect token approvals before confirm
If approval is unlimited and unnecessary, reject and retry with a limited approval amount.
7) Screenshot and log suspicious prompts
Save evidence (URL, timestamp, wallet prompt text). This helps team reporting and incident response.
Common Failure Patterns (and Better Defaults)
-
Failure: "It came from the official Discord, so it's safe."
Default: Treat every channel as compromisable; verify through a second channel. -
Failure: "The URL looks right at a glance."
Default: Compare character-by-character for high-impact actions. -
Failure: "I can revoke later."
Default: Minimize approvals now; revocation is backup, not first line defense. -
Failure: "My friend sent it, so I trusted it."
Default: Assume account takeover is possible; verify independently.
Account-Level Guardrails That Reduce Blast Radius
Even if you click once by mistake, these controls can limit damage:
- Use a hot wallet for daily interactions and a separate cold wallet for long-term holdings.
- Keep only operational funds in hot wallets.
- Enable hardware wallet confirmation for meaningful value transfers.
- Set calendar reminders to review and revoke stale approvals.
- Separate identities: different wallets for trading, governance, and public activity.
Incident Trigger: What To Do If You Signed Something Suspicious
If you think you approved a malicious action:
- Move remaining assets to a clean wallet immediately.
- Revoke approvals from a trusted interface you open from your own bookmark.
- Rotate passwords and sessions on connected accounts (email, exchange, social).
- Document addresses, tx hashes, and timestamps.
- Warn teammates/community with concrete indicators (malicious domain, contract, message screenshot).
Speed matters, but order matters too. Panic clicks can create a second loss.
Build the Habit, Not the Hype
You do not need perfect intelligence feeds to avoid most phishing. You need a friction-friendly habit you can run every day.
The Two-Channel Rule plus a 90-second checklist will prevent more losses than any "alpha" security thread. If you use a privacy access layer such as TaoFlow, treat it as one part of defense-in-depth, not a substitute for verification discipline.
Stay methodical. In crypto, boring habits are often your best security edge.