Most crypto losses are not caused by broken cryptography. They happen because normal daily workflows slowly drift into unsafe defaults: one browser profile for everything, random extension installs, hot wallet use on travel Wi-Fi, seed backups photographed for convenience, and no clear response plan when something feels wrong.
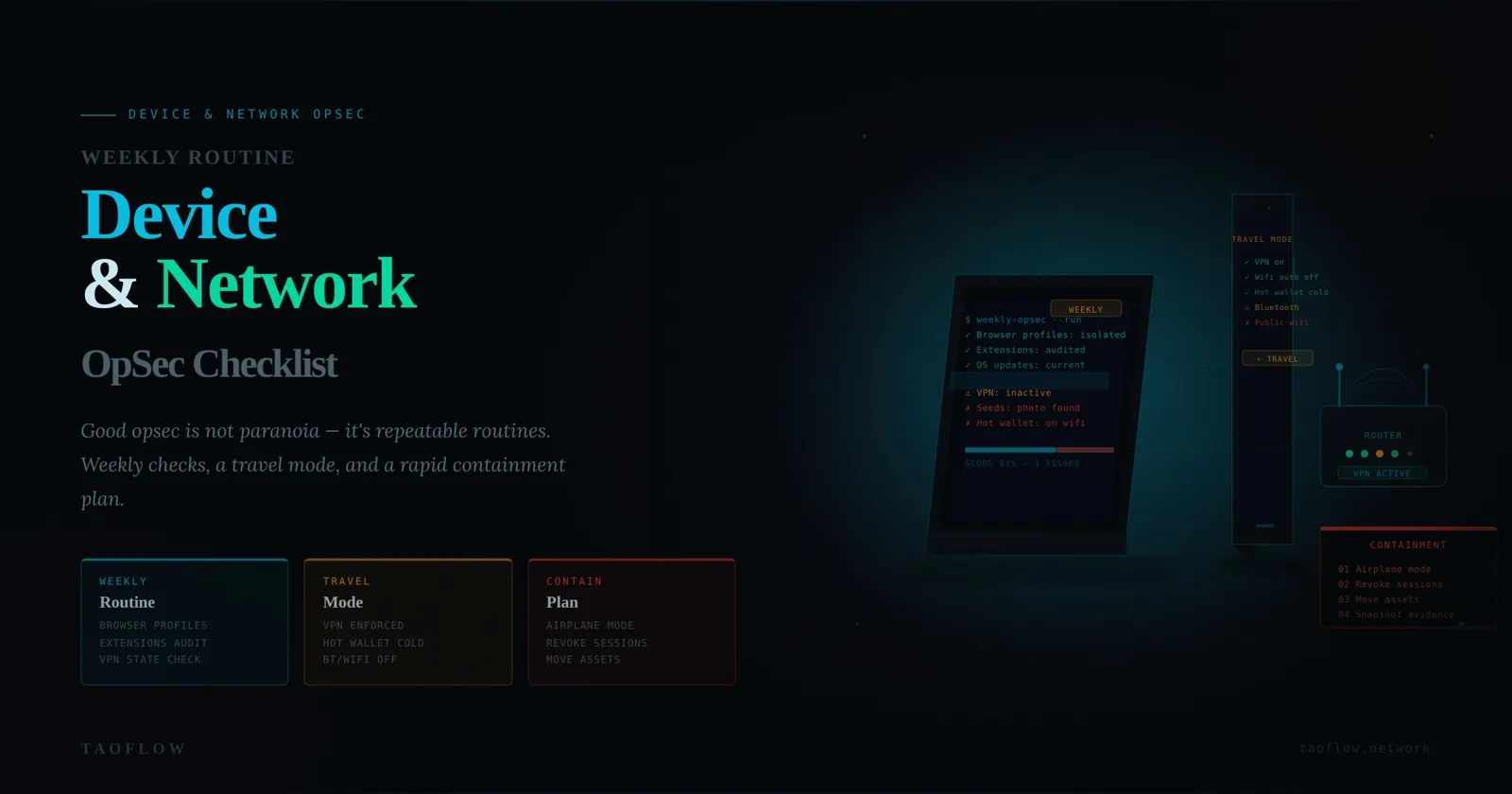
Good operational security (OpSec) does not require paranoia. It requires repeatable routines. This guide gives you a practical device-and-network checklist you can run weekly, plus a travel mode and a rapid containment plan for suspicious events.
Threat model first: what are you defending against?
For most users, the realistic threats are:
- Credential theft (phishing pages, fake wallet popups, malicious QR links).
- Session hijack (stolen browser cookies, compromised extension, reused device state).
- Endpoint compromise (malware, remote access trojan, clipboard hijacker).
- Network-level surveillance or tampering (unsafe public Wi-Fi, DNS manipulation, captive portal abuse).
- Cross-context leakage (identity linking between personal accounts and wallets through metadata).
Your goal is not perfect secrecy. Your goal is to reduce blast radius so one mistake does not become total loss.
Core principle: split your crypto life into security zones
Treat devices and browser contexts like security zones, not convenience tools.
- Zone A (Cold/Admin): high-value wallet administration, seed handling, hardware wallet firmware checks.
- Zone B (Warm/Operations): routine transactions, bridging, swaps, governance actions.
- Zone C (Hot/Experimental): testing dApps, airdrops, unknown links, social campaigns.
Do not merge zones “just for today.” Most incidents start with that sentence.
Minimum viable setup:
- Separate browser profiles per zone.
- Separate wallet accounts per zone.
- Separate bookmarks for trusted destinations in each profile.
- Strict transfer policy: funds move from A -> B -> C only with deliberate review.
Weekly 30-minute device hardening routine
Run this once per week at a fixed time. Put it on your calendar.
1) Patch state and restart discipline (5 minutes)
- Apply OS security updates on laptop/desktop/phone.
- Update browser and wallet extension only from official sources.
- Reboot after updates (many users skip this and keep old vulnerable processes alive).
Pass condition: all crypto devices fully patched and restarted in last 7 days.
2) Extension and process audit (7 minutes)
- Open extension list for each crypto browser profile.
- Remove anything not essential.
- Verify publisher names for remaining extensions.
- Check running startup items/processes for unknown entries.
Red flags: typo-brand extensions, “coupon/helper” add-ons, random PDF tools, AI sidebars with full-page access.
Pass condition: only necessary, known extensions remain.
3) Account/session hygiene (6 minutes)
- Log out of inactive exchange and tool sessions.
- Revoke stale API keys, bot tokens, and wallet connections.
- Review security logs where available (new device logins, unusual locations).
Pass condition: no stale privileged sessions; no unexplained logins.
4) DNS and network sanity checks (6 minutes)
- Confirm trusted DNS resolver settings (or encrypted DNS if you use it).
- Forget previously joined public Wi-Fi networks you do not need.
- Verify firewall is enabled on all active devices.
- Confirm auto-join for open networks is disabled.
Pass condition: no unknown remembered networks; no open auto-join behavior.
5) Backup integrity quick check (6 minutes)
- Confirm seed backups are offline and physically protected.
- Verify emergency contacts/procedure location (if applicable).
- Confirm recovery instructions are readable and up to date.
Pass condition: you can explain recovery steps from memory and locate backup materials quickly.
Network rules that prevent common failures
Rule 1: Never perform high-value signing on unmanaged public Wi-Fi
If you cannot avoid public networks, switch to low-risk read-only tasks (research, watching markets) and defer signing.
Rule 2: Use “transaction windows”
Do not sign randomly all day. Define a short, intentional window for transactions. This reduces exposure and helps you notice anomalies.
Rule 3: Verify destination and intent on two surfaces
Before sending significant funds:
- Verify recipient address from your trusted address book.
- Verify on hardware wallet screen (not only browser popup).
- Verify transaction intent (token, amount, chain, contract method).
Rule 4: Prefer typed/bookmarked domains over search-discovered links
Search ads and spoofed domains remain a top phishing vector. Use bookmarks created from verified official sources.
Rule 5: Separate “exploration” from “execution”
Browse unknown dApps in hot zone only. Execute meaningful transactions in warm zone after explicit re-verification.
Travel mode: temporary policy for higher-risk environments
When traveling, assume more hostile network conditions and reduced attention. Enable temporary stricter rules:
- Lower daily transfer limits.
- Disable nonessential wallet extensions/apps.
- Use fresh browser profile for the trip if possible.
- Avoid seed phrase handling entirely during travel.
- Delay contract approvals unless urgent and verified.
After returning:
- Revoke approvals granted during travel.
- Rotate key account passwords and passkeys where practical.
- Audit device logs and new app installs.
Metadata hygiene on devices and networks
Even when funds are safe, metadata can expose your behavior pattern.
Reduce linkability by default:
- Keep personal social browsing separate from wallet operations.
- Avoid posting transaction timing in real time.
- Do not reuse the same ENS/name/address in every context.
- Limit clipboard history sync across personal and crypto devices.
If your workflow uses privacy connectivity tooling such as TaoFlow, treat it as one layer in a broader defense stack, not a substitute for endpoint hygiene.
Incident triggers: when to stop and contain
Immediately pause activity and switch to containment mode if any of these happen:
- You signed a transaction you did not fully understand.
- Browser redirects to unexpected wallet prompts.
- Extension list changes unexpectedly.
- Clipboard address changes after copy/paste.
- New login alerts from unknown locations/devices.
First 20-minute containment playbook
- Disconnect network on suspected device.
- Move funds from potentially exposed hot/warm wallets to pre-prepared safe destination using clean device path.
- Revoke approvals for impacted addresses using trusted tools.
- Rotate credentials for email, exchange, and password manager from clean device.
- Document timeline (what was clicked/signed and when).
Do not keep “testing” the compromised environment. Preserve evidence and isolate it.
Practical baseline stack (no brand dependency)
- Hardware wallet for high-value signing.
- Password manager with unique random credentials.
- Passkeys or strong MFA for critical accounts.
- Separate browser profiles for security zones.
- Weekly patch and extension audit routine.
- Written incident response checklist.
This baseline outperforms most “advanced” setups that lack discipline.
A simple scorecard to track your OpSec maturity
Rate each item 0 (no), 1 (partial), 2 (consistent):
- Zone separation enforced (A/B/C).
- Weekly update + reboot complete.
- Extension footprint minimal and verified.
- Public Wi-Fi signing policy enforced.
- Two-surface transaction verification used.
- Backup integrity tested in last 30 days.
- Incident playbook documented and accessible.
0-5: high risk from routine failures. 6-10: improving but inconsistent habits. 11-14: resilient day-to-day posture.
Re-score monthly and focus only on the weakest two controls first.
Final takeaway
Crypto security is less about one perfect tool and more about predictable behavior under normal stress. If you build clear security zones, run a short weekly routine, and practice containment before an incident happens, you dramatically reduce both probability and impact of loss.
Start with one commitment this week: schedule your 30-minute routine and keep it for four consecutive weeks. Consistency is your strongest defense.